Before You Begin
Before creating a Generic Webhook Alert Source, make sure you have:- Access to create alert sources in Rootly
- A tool that can send
POSTrequests with a JSON body - A plan for how alerts should be routed after ingestion
- The fields you want Rootly to extract, such as:
- Alert title
- Description
- External identifier
- Alert state
- Routing target
Content-Type: application/json.
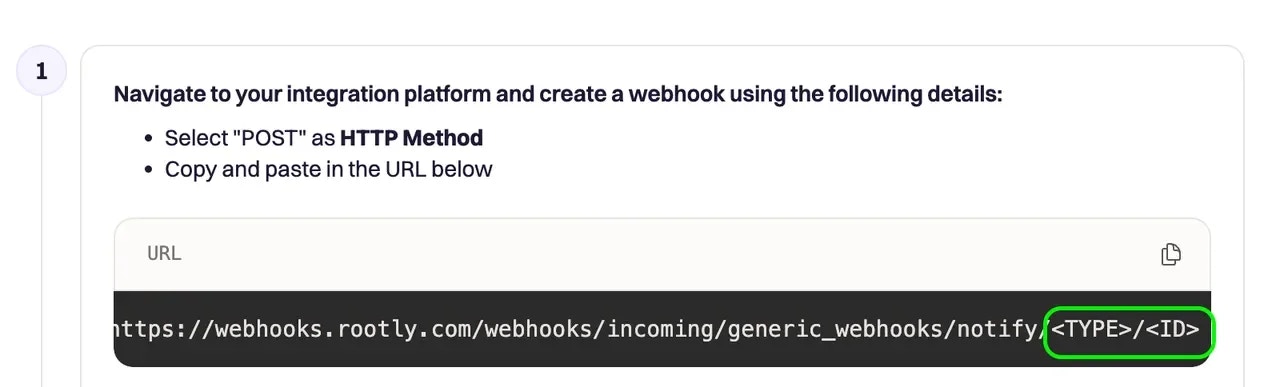
In production, the Generic Webhook Alert Source uses these endpoint patterns:
- Base endpoint:
POST https://webhooks.rootly.com/webhooks/incoming/generic_webhooks - Fixed target endpoint:
POST https://webhooks.rootly.com/webhooks/incoming/generic_webhooks/notify/<type>/<id>
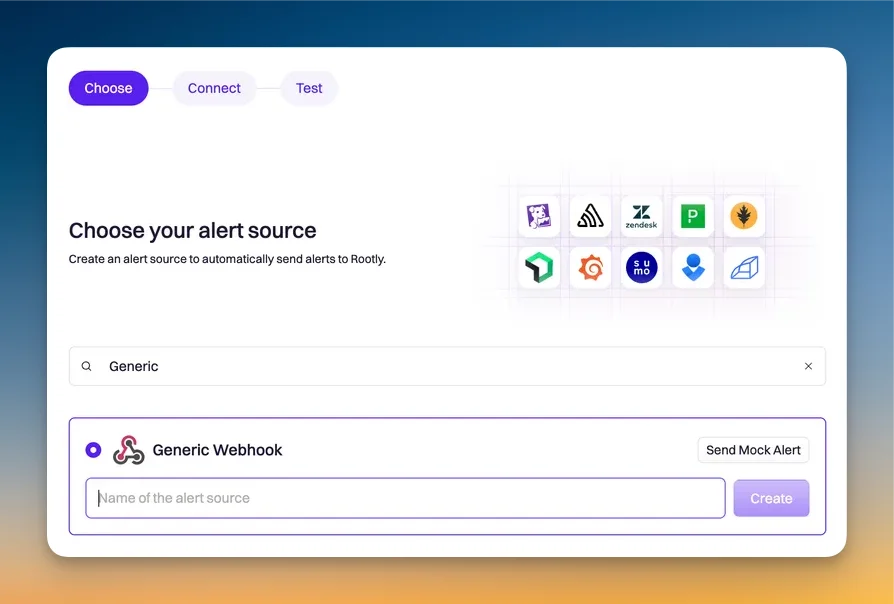
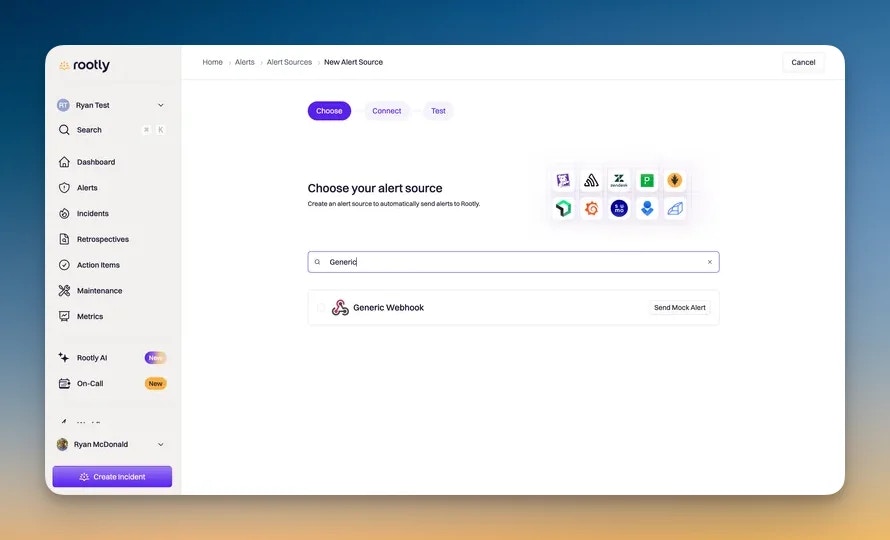
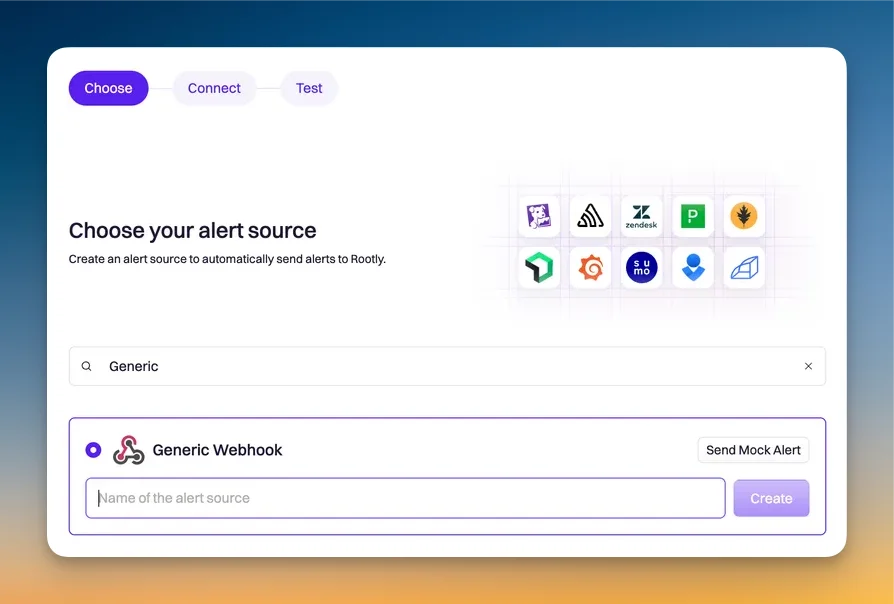
Create and Configure the Source
Create the Generic Webhook Alert Source
Go to the new alert source page and locate Generic Webhook Alert Source.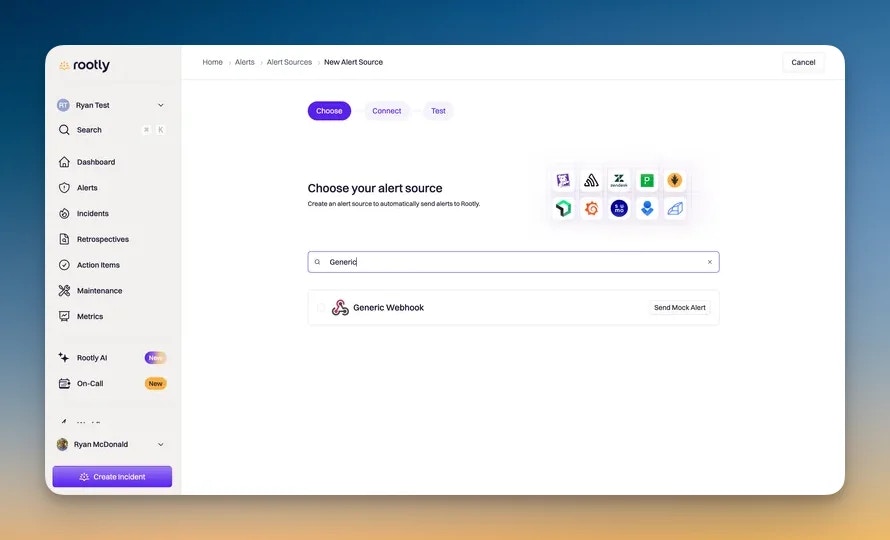
Authenticate incoming requests
Rootly supports two authentication methods for incoming generic webhook requests: Bearer Token and HMAC Signature.HMAC provides a stronger authentication model where the signing secret never travels over the wire. Instead, the sender signs the request body and Rootly verifies the signature.When you select HMAC Signature as the authentication type during source creation, Rootly generates a signing secret for you. Your external system must use this secret to sign every request.To configure HMAC authentication:Example (Node.js):
Bearer Token (default)
With Bearer Token authentication, Rootly verifies the request using a static secret. You can provide the secret in either of these ways:Authorization: Bearer <secret>secretas a query string or request parameter
HMAC Signature
HMAC signature authentication must be enabled for your organization. Contact Rootly support to enable it.
- Select HMAC Signature as the authentication type when creating or editing the source
- Copy the HMAC Signing Secret shown in the setup instructions
- For each request, compute the signature over the raw request body:
- Include the signature in the
X-Webhook-Signature-256header
X-Webhook-Signature-256 header is missing or the signature does not match, Rootly returns a 401 Unauthorized response.Example (Python):Map the incoming payload fields
Generic webhook sources do not require a strict vendor-specific payload shape. Instead, you configure how Rootly should interpret the incoming JSON by mapping fields from the webhook payload.At a minimum, you should map a field for the alert title so alerts are easy to identify in Rootly.Depending on your use case, you may also want to map:
- Alert description
- External URL
- External identifier
- Alert state
- Notification target type
- Notification target ID
Configure Routing Targets
There are two main ways to tell Rootly where an alert should route.Set the target in the webhook URL
This is the simplest option when each webhook should always route to the same target.With this approach, you include the target type and target ID in the webhook URL. This is useful when alerts from a given source should always be associated with the same service, team, escalation policy, or other supported target.Common target types include: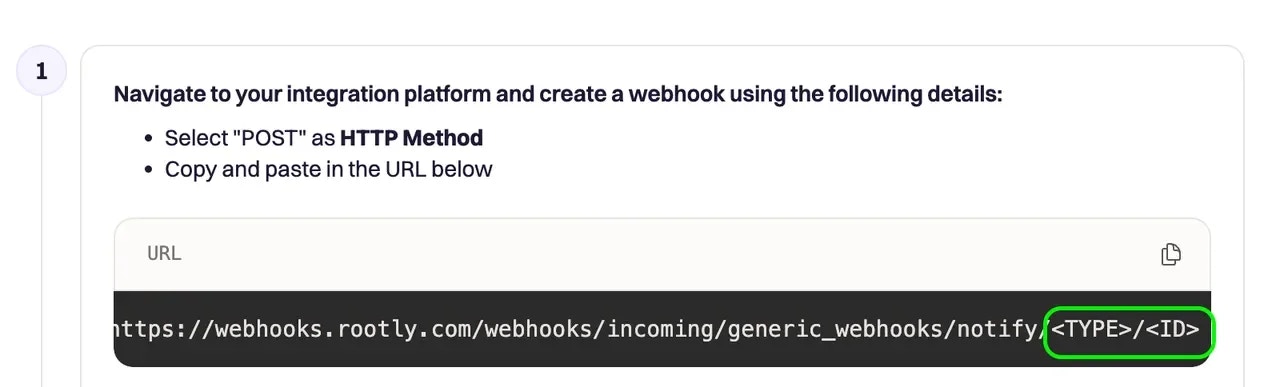
servicegrouporteamescalationPolicy
Set the target from the incoming payload
This option is more flexible when the same webhook source may need to route alerts to different targets.With this approach, your external system sends the target information in the webhook JSON body, and Rootly extracts it using your configured field mappings.Use this option when:
- A single source may route alerts to different services or teams
- Your observability tool already includes routing metadata in the webhook body
- You want the routing decision to come from the event payload itself
Test the Source
Send a test alert
After setup, send a test alert from your observability provider and confirm that Rootly receives and processes it as expected.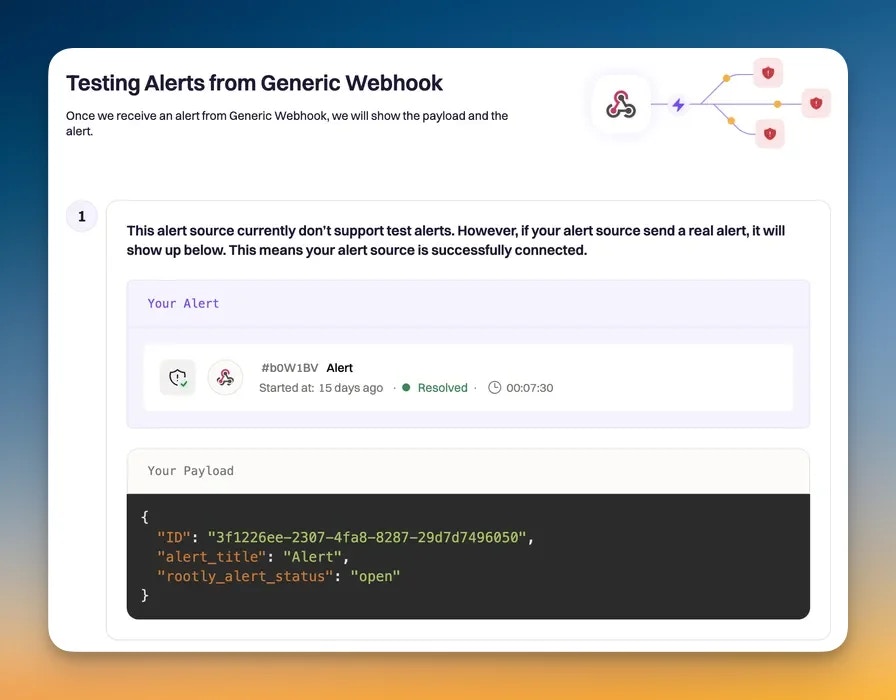
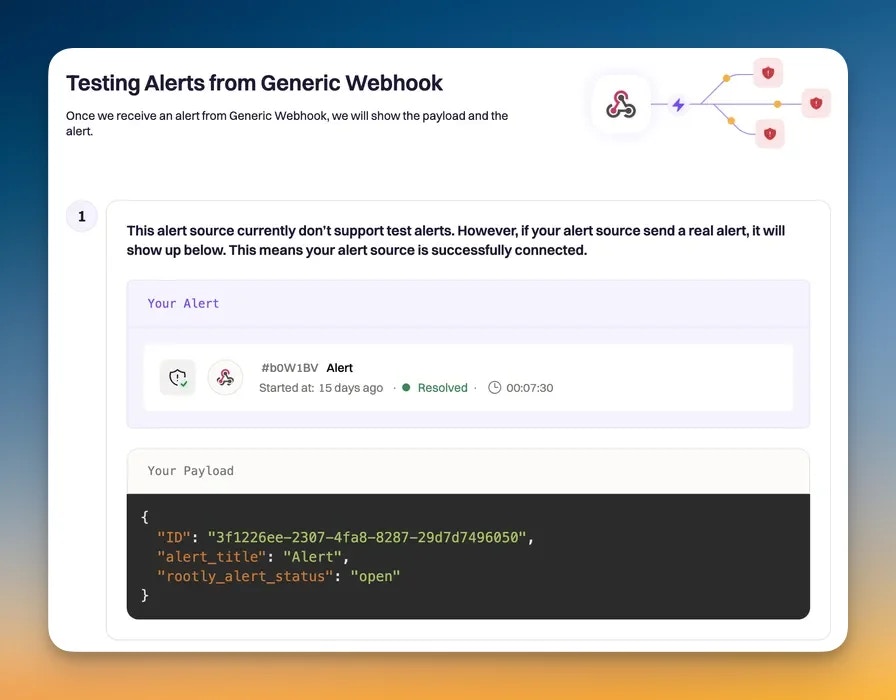
Confirm the alert was processed correctly
A successful test should confirm that:
- The webhook request reaches Rootly
- The payload is parsed correctly
- The alert title and other mapped fields are populated as expected
- The alert routes to the correct target
- The alert appears in Rootly
Next Steps
Auto-Resolution
Configure Rootly to resolve alerts automatically when your source sends recovery events.
Alert Workflows
Automate incidents, notifications, and follow-up actions for alerts created through this source.